They say blockchains are like onions. Onions have layers. Blockchains have layers. The symbiotic relationship between Ethereum and its Layer 2s is mutualistic, meaning the two both benefit from the relationship. Ethereum provides its ever important security to the Layer 2s within its ecosystem, meaning those Layer 2s settle their transactions at the Ethereum Layer 1 level. How do they do this? What does it mean for Layer 2s to rely on Ethereum for its “Security”? To understand this, we first need to dive into the Blockchain Trilemma.
The Blockchain Trilemma
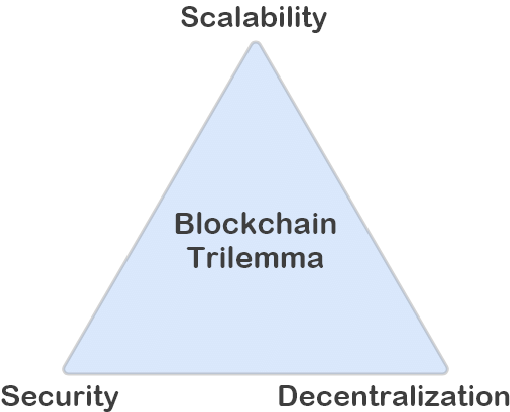
Before we understand why Layer 2 solutions are critical to the Ethereum ecosystem, there is an important concept to understand called “The Blockchain Trilemma”. The Blockchain Trilemma refers to the commonly held notion that decentralization, security and scalability are the three pillars on which blockchain fundamentally rests, and that decentralized networks can only provide two of the three benefits at any given time. The widely held notion is that public blockchain infrastructure must sacrifice security, decentralization or scalability.
Decentralization is the central ethos of blockchain technology and drives projects across the ecosystem. Blockchain decentralization refers to the meaningful distribution of computing power and consensus throughout a network. Applying decentralized processes and tech eliminates the role of intermediaries across industries and manifests in many different ways. For example: by removing banking institutions from financial instruments, decentralized finance (DeFi) platforms, rather than intermediaries, are able to distribute profits and governance to users and the wider community.
On an even more foundational level, decentralized networks crowdsource consensus, meaning that no one entity can control or censor the data that transacts through it. However, achieving optimal decentralization tends to decrease network throughput. As more miners secure a Proof of Work (PoW) network through consensus, transaction speeds may drop — which is considered a hurdle to widespread adoption.
Security reflects a blockchain protocol’s defenses against malicious actors and network attacks. To increase network throughput on a blockchain network, there's an incentive to reduce the distribution of blockchain nodes either geographically, in number, or both. However, this pivot toward greater centralization reduces security on PoW networks. When consensus is achieved on an open network with limited nodal distribution, a 51% attack is more probable as hackers can amass the required hashing power with greater ease. By overwhelming a network, hackers can hijack the network and manipulate transactions for financial gain. For example: In August 2020, the Ethereum Classic (ETC) blockchain — which is a fork of Ethereum (ETH) — suffered three 51% attacks that reorganized more than 4,000 blocks. This allowed the perpetrators to manipulate data and double spend its ETC currency, resulting in the loss of millions of dollars in value on the network. Blockchain security is a critical network aspect that cannot be compromised.
Scalability with regard to a blockchain protocol refers to the blockchain’s ability to support high transactional throughput and future growth. This means that as use cases and adoption accelerate, the performance of the blockchain won’t suffer. Blockchains that perform poorly as adoption increases are said to lack scalability. The Blockchain Trilemma tells us that greater scalability is possible, but security, decentralization, or both, will suffer as a consequence. Scalability is the only way for blockchain networks to reasonably compete with the current centralized payment platforms whose network settlement times and usability are, at this point, far superior.
Looking at Ethereum specifically, the focus of the network was on decentralization and security, with the number of transactions per second (scalability) being limited. To encourage miners to prioritize their transactions, users paid higher fees. As demand for block space grows and Ethereum gets more popular, to the increased demand, transaction fees have risen to the point where some people cannot engage with the blockchain. Increased Ethereum fees are a byproduct of the trilemma, as we can see that Ethereum was not able to cheaply scale without sacrificing security or decentralization.
Scalability improvements can occur both at the Layer 1 and Layer 2 level. Layer 1 scaling solutions create changes to the base layer of the blockchain protocol itself in order to improve scalability, whereas Layer 2 solutions build on top of the existing Layer 1 to reduce the workload that the Layer 1 needs to reach consensus, therefore using less resources.
Now that we have a better grasp of the problem, let's take a step back and define the different layers of a Blockchain.
Layer 1
A Layer 1 network is another name for a base blockchain. Ethereum (ETH), Bitcoin (BTC), BNB Smart Chain (BNB), Solana (SOL), Avalanche (AVAX) and Fantom (FTM) are all Layer 1 protocols (amongst others). We refer to them as Layer 1 because these are the main networks within their ecosystem. In contrast to Layer 1, we have off-chains and other Layer 2 solutions that are built on top of the main chains.
A Layer 1 network is ultimately responsible for the settlement of transactions. For most network’s this means accounting for a user’s account, or wallet, via asymmetric key pairs and its corresponding cryptocurrency or token balances. All Layer 1 networks have a native token that provides access to the network's resources. You use a network's native token to pay for network services like sending its cryptocurrency, minting a token, or calling a smart contract.
When comparing Layer 1 networks, it is essential to learn about its consensus mechanism and the pros or cons that it provides. The consensus mechanisms involved generally have trade-offs between transaction cost, security, scalability, and decentralization. There is a lot of innovation in consensus mechanisms and is a field that is constantly evolving and contributing to the array of blockchains known today.
Working on scalability improvements does not only occur at the Layer 2 level, however. Layer 1 scaling solutions augment the base layer of the blockchain protocol itself in order to improve scalability. A number of methodologies are currently being developed — and practiced — that improve the scalability of blockchain networks directly. Here’s how it works:
Layer 1 solutions change the rules of the protocol directly to increase transaction capacity and speed, while accommodating more users and data.
Layer 1 scaling solutions can entail, for example, increasing the amount of data contained in each block, or accelerating the rate at which blocks are confirmed, so as to increase overall network throughput.
Easy enough? Unfortunately not
The problem with increasing block size or accelerating the rate at which blocks are confirmed is that it then requires computational power well beyond the standard home computer to run a node, which in turn leads to less access to the ability to run a decentralized node, which leads to more centralized nodes being created by larger actors, which leads to the few being able to exert more control over the system, which decreases security.
Remember those three desirable properties of a blockchain? Decentralization, Security, and Scalability? The blockchain trilemma states that a simple blockchain architecture can only achieve two out of three. Want a secure and decentralized blockchain? You need to sacrifice scalability. So what can you do to make upgrades at the Layer 1 level keeping this in mind?
Consensus protocol improvements
Some consensus mechanisms are more efficient than others. PoW is the consensus protocol currently in use on popular blockchain networks like Bitcoin. Although PoW is secure, it can be slow. That’s why many newer blockchain networks favor the Proof of Stake (PoS) consensus mechanism. Instead of requiring miners to solve cryptographic algorithms using substantial computing power, PoS systems process and validate new blocks of transaction data based on participants staking collateral in the network.
We discussed The Merge, the event where Ethereum changes from a PoW consensus mechanism to a PoS consensus mechanism, in a prior article you can read here.
Sharding
Sharding is a mechanism adapted from distributed databases that has become one of the most popular Layer 1 scaling solutions, despite its somewhat experimental nature within the blockchain sector. Sharding entails breaking the state of the entire blockchain network into distinct datasets called "shards" — a more manageable task than requiring all nodes to maintain the entire network. These network shards are simultaneously processed in parallel by the network, allowing for sequential work on numerous transactions.
Further, each network node is assigned to a particular shard instead of maintaining a copy of the blockchain in its entirety. Individual shards provide proofs to the mainchain and interact with one another to share addresses, balances, and general states using cross-shard communication protocols. Ethereum is one high-profile blockchain protocol that is exploring shards, along with Zilliqa, Tezos, and Qtum.
Ethereum has reached the network's current capacity with 1+ million transactions per day and high demand for each of these transactions. The success of Ethereum, the strength of its community, and the demand to use it has caused gas prices to rise substantially. Therefore, the need for additional scaling solutions outside of Ethereum Layer 1 has increased in demand as well.
This is where Layer 2 networks come in.
Layer 2
Layer 2 is a collective term for Ethereum scaling blockchain networks which extend the functionality of Ethereum (or another Layer 1) by handling transactions off of Ethereum Layer 1 while still taking advantage of the decentralized security of Ethereum Layer 1. This can be to increase the Layer 1 network’s performance, reduce transaction fees, or increase programmability. For example, on Ethereum, where gas fees can be highly variable and transaction times slow, it is increasingly common for application developers to provide its user the ability to interact with a Layer 2 network to decrease their user’s fees and transaction latency.
A Layer 2 blockchain regularly communicates with Ethereum (by submitting bundles of transactions) in order to ensure it has similar security and decentralization guarantees. All this requires no changes to the Layer 1 protocol (Ethereum). This lets Layer 1 handle security, data availability, and decentralization, while Layer 2s handles scaling. Layer 2s take the transactional burden away from Layer 1 and post finalized proofs back to Layer 1. By removing this transaction load from Layer 1, the base layer becomes less congested, and everything becomes more scalable. Further, as the Layer 1 implements new protocols that help it scale (such as Ethereum moving to a Proof of Stake consensus mechanism (“The Merge”) followed by implementing sharding, which would increase Ethereum’s capacity exponentially) the Layer 2’s will benefit and in turn increase in speed/capacity based on the order of magnitude that they have already scaled the base Layer 1.
Layer 3
Layer three blockchain protocols, or the decentralized application (dApp) layer of blockchain, can be split into two major sub-layers — application and execution — depending on a given dApp’s use case.
The application sub-layer deals with user-facing applications meant to facilitate user interactions with a blockchain, for which the main components are APIs, user interfaces (UIs), and scripts. dApps in this category interact with the base blockchain using APIs.
On the other hand, the execution layer handles the rules and smart contracts. As such, it holds the actual application juice, which is the code. The intersection between the two layers appears during execution. For example, when a user initiates a token swap on a DEX using the application layer, the transaction then goes to the execution layer to be processed.
Layer 0
A Layer 0 protocol can be used across several use cases, including data validation, setting up individual reward structures, digital currency wrapping and more. It serves as a root layer, allowing cross-chain interoperability with all Layer 1 protocols like BTC, ADA, Ethereum and more. We won't be focusing on Layer 0 here, but it is good to know the basics. We will come back to this at some point!
Now that we understand what the parts are conceptually, let's dive a little deeper into how they work.
Layer 2 blockchain operates on the native layer to improve its efficiency. Effectively offloading transactions, Layer 2 takes a portion of Level 1 blockchain’s transactional burden and gives it to another system architecture. The Layer 2 blockchain then handles the processing load and reports to Layer 1 for result finalization. Since most of the data processing load is given to this adjacent auxiliary architecture, network congestion is reduced: not only does the Layer 1 blockchain become less congested, it also becomes more scalable.
So what are some examples of Layer 2s?
State Channels
State channels are mechanisms used to allow users to directly conduct operations with each other on a layer outside a blockchain (off-chain). They only report the results to the blockchain when a channel closes. A great example of a layer two protocol that uses state channels is the Lightning Network on Bitcoin.
Lightning Network is a layer two payment channel operating on top of the Bitcoin blockchain, which aims to process multiple small transactions off-chain in order to decongest the main chain, freeing it up for larger transactions.
Plasma
Plasma is a scaling solution for the Ethereum blockchain. Unlike Bitcoin’s Lightning Network, Plasma takes a different approach, as it provides a generalized framework that supports the creation of other “child chains” powered by Ethereum. Plasma employs Merkle Trees plus smart contracts to create what are essentially stripped-down versions of Ethereum. Unfortunately, the original Plasma model was never implemented and Ethereum is now focusing on other layer two solutions like rollups.
In Ethereum’s case, the applications running on top of it are constantly exhausting its network capacity, causing bottlenecks. Layer two solutions are aimed to decongest the network in order to overcome high fees and slow confirmation times.
Rollups (Optimistic and Zero Knowledge)
Rollups are a scaling solution that work by rolling up (hence the name) collections of transactions. The final, rolled-up transaction is presented to the Ethereum blockchain as a single transaction.
Rollups cuts costs: the cost of an Ethereum transaction, plus the small cost of rolling up batches of transactions, is split among users. They also speed things up: the rollup is very quick to perform and the Ethereum blockchain needs only to process a single transaction rather than many. That's useful when Ethereum maxes out at around 15 transactions per second unassisted.
There are two main types of rollups: optimistic rollups and zero-knowledge rollups.
Optimistic Rollups
Optimistic rollups sit in parallel to the main Ethereum chain on layer 2. They can offer improvements in scalability because they don't do any computation by default. Instead, after a transaction, they propose the new state to Mainnet or "notarize" the transaction.
With Optimistic rollups, transactions are written to the main Ethereum chain as calldata, optimizing them further by reducing the gas cost.
As computation is the slow, expensive part of using Ethereum, Optimistic rollups can offer up to 10-100x improvements in scalability dependent on the transaction. This number will increase even more with the introduction of sharding that we mentioned previously as more data will be available if a transaction is disputed.
Disputing transactions
Optimistic rollups don't compute the transaction, so there needs to be a mechanism to ensure transactions are legitimate and not fraudulent. This is where fraud proofs come in. If someone notices a fraudulent transaction, the rollup will execute a fraud-proof and run the transaction's computation, using the available state data. This means you may have longer wait times for transaction confirmation than a ZK-rollup because the transaction could get challenged.
The gas you need to run the computation of the fraud proof is even reimbursed. Ben Jones from Optimism describes the bonding system in place:
Anyone who might be able to take an action that you would have to prove fraudulent to secure your funds requires that you post a bond. You basically take some ETH and lock it up and you say "Hey, I promise to tell the truth"... If I don't tell the truth and fraud is proven, this money will be slashed. Not only does some of this money get slashed but some of it will pay for the gas that people spent doing the fraud proof. - Ben Jones
So you can see the incentives: participants get penalized for conducting fraud and reimbursed for proving fraud.
Zero-Knowledge (zk) Rollups
A demonstration of zero knowledge must meet the following three requirements:
Irrefutability: If the claim is genuine, an honest prover will be persuaded of its integrity by an equally honest verifier (i.e., one correctly following the protocol).
Soundness: If the claim is untrue, there is only a slim chance that the dishonest prover can persuade the honest verifier that it is.
Zero-Knowledge: If the claim is accurate, the only thing the verifier knows is that the claim is valid.
ZK-rollups bundle hundreds of transfers off-chain and generate a cryptographic proof. These proofs can come in the form of SNARKs (succinct non-interactive argument of knowledge) or STARKs (scalable transparent argument of knowledge). One of the main components that allow zk-rollups to successfully validate transactions faster than Layer 1 blockchains are Merkle Trees.
Merkle Trees are an important mathematical structure that allow blockchains to ensure that no one can fake data in the on-chain records of a zk-rollup. Usually, a zk-rollup consists of two Merkle Trees which are both stored on a smart contract, or in other words, on-chain. One tree is dedicated to storing accounts, while the other stores all balances. Any other type of data generated and used by the zk-rollup is stored off-chain.
Unlike optimistic rollups that force transactions to wait a period of time for fraud proofs, when a ZK-SNARK is sent to Ethereum the receiving smart contract can instantly verify if the proof is valid or not on-chain.
Because ZK-SNARKs are verified instantly, funds are able to be withdrawn on ZK-rollups as soon as the ZK-SNARK transaction is mined on Ethereum (~12 seconds), rather than waiting days or weeks for the dispute period to end.
Validity proofs prevent fraud without manual intervention or verification like fraud proofs, which makes transaction confirmation with ZK-rollups much faster and scalable than optimistic rollups.
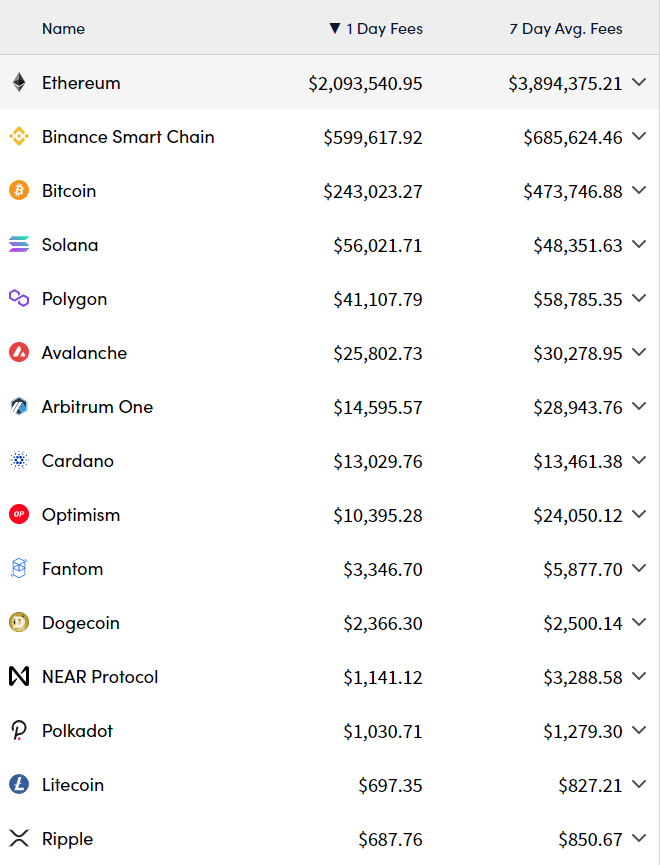
In future articles we will take a deep dive into the different Layer 2 technologies and the companies working on implementing them. For now, the key takeaway that I want you to leave here with is that, while you may hear about the next Ethereum killer being spun up with a massive raise behind it almost by the month, statistics do not lie. The numbers in the table above show that the vast, vast majority of fees earned in Web3 are earned in the Ethereum Ecosystem. Ethereum is nearly 4 times larger than the next largest chain in terms of fee earnings, and earns more on a daily basis than every other chain listed, combined according to the chart from CryptoFees.info.
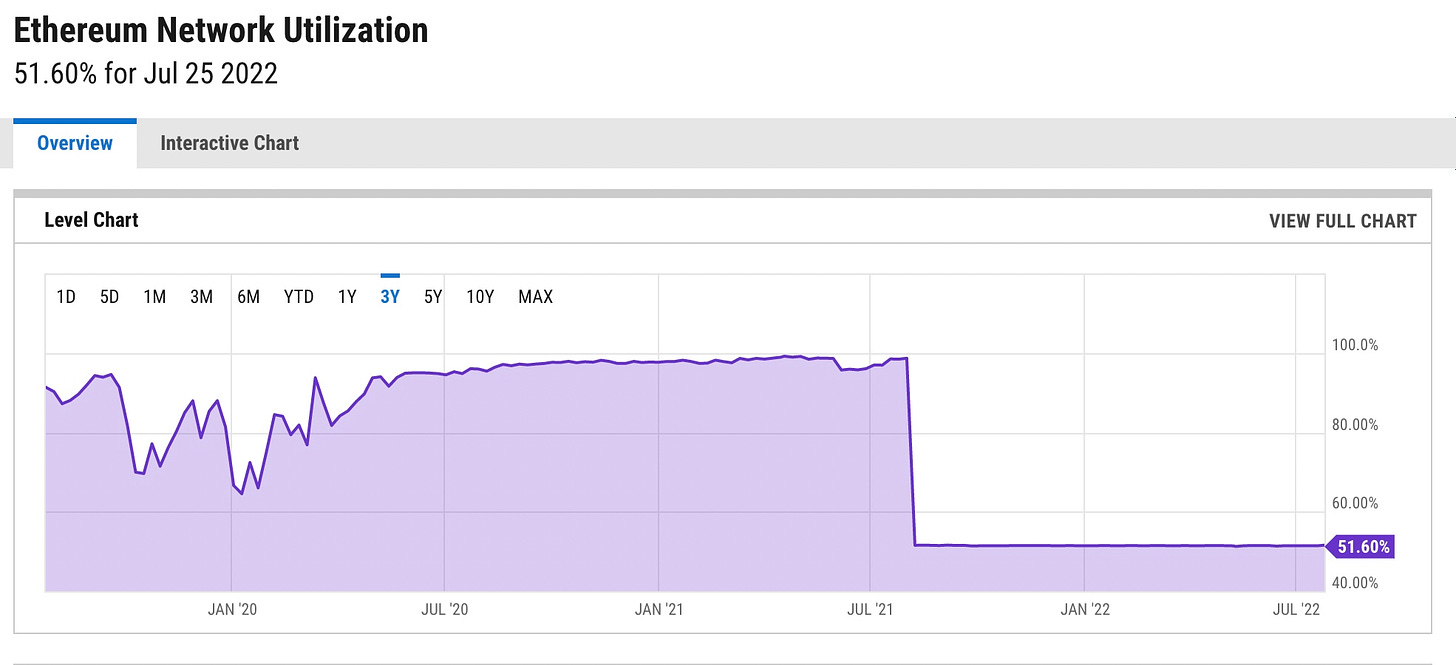
We can see in the charts above, taken from ycharts that even with the spikes in gas fees over the course of the last 3 years, network utilization remained constantly near the upper limits of the networks abilities (In August 2021, Ethereum implemented its London hard fork, which doubled block size, but also capped the usage at its throughput at that time at the 51.6% constant you see above to reduce the overall network load, which is why it cuts in half on the chart above). This shows that even when there are cheaper or faster options, the Ethereum network still has demand. This is a testament to its strong community, and only highlights the case for Layer 2s even more as history has shown that even when gas prices were at their highs, the Network’s utilization remained high. This, in my opinion, is a strong indicator that users and developers will be far more likely to choose to develop on the Layer 2 that suits their needs the best, while still being able to avail themselves of Ethereum’s security and decentralization.
Further, if you take a look at the daily fee chart above closely, you will see that this hypothesis is starting to be tested and is holding up relatively well. After Ethereum, 3 of the largest remaining 9 fee earners in the top 10 are Layer 2s within the Ethereum ecosystem (Polygon, Arbitrum and Optimism). The more ETH Grows, the more it needs Layer 2s. The more Layer 2s grow, the more I believe ETH in turn grows because the Layer 2s increase its overall capacity and compete for the ever increasingly valuable Ethereum block space. As I mentioned at the beginning of this article, it truly is a mutually symbiotic relationship.
Not financial, legal or tax advice. This newsletter is strictly educational and is not investment advice or a solicitation to buy or sell any assets or to make any financial decisions. All opinions expressed are solely those of the individual author. This newsletter is not legal advice and does not create an attorney-client relationship. This newsletter does not constitute tax advice. Talk to your independent attorney and/or accountant for any questions specific to you. Always do your own research and use caution when interacting with smart contracts or the blockchain.